I have installed metasploit on a victims computer that is not connected to internet but how do I get their ip? Do I need his ip to enable webcam or something on Metasploit? I know I need it for Armitage.
- Hot
- Active
-
 Forum Thread:
How to Hack Android Phone Using Same Wifi
22
Replies
Forum Thread:
How to Hack Android Phone Using Same Wifi
22
Replies
41 min ago -
 Forum Thread:
Changing IP Address
9
Replies
Forum Thread:
Changing IP Address
9
Replies
4 days ago -
 Forum Thread:
When My Kali Linux Finishes Installing (It Is Ready to Boot), and When I Try to Boot It All I Get Is a Black Screen.
8
Replies
Forum Thread:
When My Kali Linux Finishes Installing (It Is Ready to Boot), and When I Try to Boot It All I Get Is a Black Screen.
8
Replies
1 wk ago -
 Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
2 wks ago -
 Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
2
Replies
Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
2
Replies
1 mo ago -
 Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
1 mo ago -
 Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
3 mo ago -
 Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
3 mo ago -
 Metasploit Error:
Handler Failed to Bind
41
Replies
Metasploit Error:
Handler Failed to Bind
41
Replies
3 mo ago -
 How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
3 mo ago -
 How to:
Crack Instagram Passwords Using Instainsane
36
Replies
How to:
Crack Instagram Passwords Using Instainsane
36
Replies
3 mo ago -
 Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
3 mo ago -
 Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
4 mo ago -
 Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
5 mo ago -
 How to:
Sign the APK File with Embedded Payload (The Ultimate Guide)
10
Replies
How to:
Sign the APK File with Embedded Payload (The Ultimate Guide)
10
Replies
5 mo ago -
 Forum Thread:
How to Run and Install Kali Linux on a Chromebook
18
Replies
Forum Thread:
How to Run and Install Kali Linux on a Chromebook
18
Replies
6 mo ago -
 Forum Thread:
How to Find Admin Panel Page of a Website?
13
Replies
Forum Thread:
How to Find Admin Panel Page of a Website?
13
Replies
6 mo ago -
 Forum Thread:
can i run kali lenux in windows 10 without reboting my computer
4
Replies
Forum Thread:
can i run kali lenux in windows 10 without reboting my computer
4
Replies
6 mo ago -
 Forum Thread:
How to Hack School Website
11
Replies
Forum Thread:
How to Hack School Website
11
Replies
6 mo ago -
 Forum Thread:
Make a Phishing Page for Harvesting Credentials Yourself
8
Replies
Forum Thread:
Make a Phishing Page for Harvesting Credentials Yourself
8
Replies
7 mo ago
-
 How To:
Top 10 Things to Do After Installing Kali Linux
How To:
Top 10 Things to Do After Installing Kali Linux
-
 How To:
Use Burp & FoxyProxy to Easily Switch Between Proxy Settings
How To:
Use Burp & FoxyProxy to Easily Switch Between Proxy Settings
-
 How To:
Dox Anyone
How To:
Dox Anyone
-
 How To:
Find Identifying Information from a Phone Number Using OSINT Tools
How To:
Find Identifying Information from a Phone Number Using OSINT Tools
-
 How To:
Check if Your Wireless Network Adapter Supports Monitor Mode & Packet Injection
How To:
Check if Your Wireless Network Adapter Supports Monitor Mode & Packet Injection
-
 Tutorial:
Create Wordlists with Crunch
Tutorial:
Create Wordlists with Crunch
-
 How To:
Buy the Best Wireless Network Adapter for Wi-Fi Hacking in 2019
How To:
Buy the Best Wireless Network Adapter for Wi-Fi Hacking in 2019
-
 How To:
Embed a Metasploit Payload in an Original .Apk File | Part 2 – Do It Manually
How To:
Embed a Metasploit Payload in an Original .Apk File | Part 2 – Do It Manually
-
 How To:
Enable Monitor Mode & Packet Injection on the Raspberry Pi
How To:
Enable Monitor Mode & Packet Injection on the Raspberry Pi
-
 How To:
Set Up a Practice Computer to Kill on a Raspberry Pi
How To:
Set Up a Practice Computer to Kill on a Raspberry Pi
-
 How To:
Phish for Social Media & Other Account Passwords with BlackEye
How To:
Phish for Social Media & Other Account Passwords with BlackEye
-
 How To:
Enumerate SMB with Enum4linux & Smbclient
How To:
Enumerate SMB with Enum4linux & Smbclient
-
 How To:
Exploit WebDAV on a Server & Get a Shell
How To:
Exploit WebDAV on a Server & Get a Shell
-
 How To:
Use SpiderFoot for OSINT Gathering
How To:
Use SpiderFoot for OSINT Gathering
-
 How To:
Create Rainbow Tables for Hashing Algorithms Like MD5, SHA1 & NTLM
How To:
Create Rainbow Tables for Hashing Algorithms Like MD5, SHA1 & NTLM
-
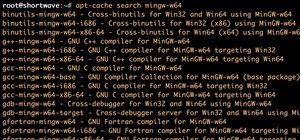
 How To:
Use MinGW to Compile Windows Exploits on Kali Linux
How To:
Use MinGW to Compile Windows Exploits on Kali Linux
-
 How To:
Brute-Force Email Using a Simple Bash Script (Ft. THC Hydra)
How To:
Brute-Force Email Using a Simple Bash Script (Ft. THC Hydra)
-
 How To:
Conduct a Pentest Like a Pro in 6 Phases
How To:
Conduct a Pentest Like a Pro in 6 Phases
-
 How To:
Host Your Own Tor Hidden Service with a Custom Onion Address
How To:
Host Your Own Tor Hidden Service with a Custom Onion Address
-
 How To:
Set Up an Eviltwin
How To:
Set Up an Eviltwin
















6 Responses
seriously dude...if u have already have access to the victim's laptop ...why do u want to hack it ..u have it in your hands
and let us assume u want to hack it ..why did u install the metasploit framewrk onn hix computer...who is going to attack the other mate ????
all u have to do is to install the metasploit to ur computer ( u r the attacker not him ) then generate a payload and send it to the victim ...u can also have the ip useing the nmap tool
hope that answers ur Q
Do I need my metasploit (or computer) running when i install the payload on their computer?
Hey there...
Metasploit is a framework of tools that can be used to exploit vulnerabilities in a system. Armitage is more or less a gui of metasploit. Neither of them are exploits or payloads themselves, but a means of finding, creating, and interacting with one.
As mentioned by mohammad, you could use metasploit to generate a payload to exploit a specific vulnerability in an OS and install that on the targets system. This would most likely require you to know your public ip address if your not on the targets LAN so the payload knows what system it should be relaying data to.
If you want to know your public ip or someone elses and have access to the machine, you can simply punch into google "whatsmyip" and it will tell you. Without access to the system or network the only thing i can suggest is social engineering.
Do I need my metasploit (or computer) running when i install the payload on their computer?
Not necessarily.. you should be able to start the listener whenever you want as long as the payload is installed and running.
is it always going to be running?
Share Your Thoughts