2) Is There a Payload That Can Access Windows 7 or 8 Without the Victim Clicking on Any Malicious Program We Send or Just Getting Direct Access to the Victim's Computer Just with RHOST and RPORT ???
- Hot
- Active
-
 Forum Thread:
Changing IP Address
9
Replies
Forum Thread:
Changing IP Address
9
Replies
15 hrs ago -
 Forum Thread:
When My Kali Linux Finishes Installing (It Is Ready to Boot), and When I Try to Boot It All I Get Is a Black Screen.
8
Replies
Forum Thread:
When My Kali Linux Finishes Installing (It Is Ready to Boot), and When I Try to Boot It All I Get Is a Black Screen.
8
Replies
1 wk ago -
 Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
2 wks ago -
 Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
2
Replies
Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
2
Replies
1 mo ago -
 Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
1 mo ago -
 Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
2 mo ago -
 Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
3 mo ago -
 Metasploit Error:
Handler Failed to Bind
41
Replies
Metasploit Error:
Handler Failed to Bind
41
Replies
3 mo ago -
 Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
3 mo ago -
 How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
3 mo ago -
 How to:
Crack Instagram Passwords Using Instainsane
36
Replies
How to:
Crack Instagram Passwords Using Instainsane
36
Replies
3 mo ago -
 Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
3 mo ago -
 Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
4 mo ago -
 Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
5 mo ago -
 How to:
Sign the APK File with Embedded Payload (The Ultimate Guide)
10
Replies
How to:
Sign the APK File with Embedded Payload (The Ultimate Guide)
10
Replies
5 mo ago -
 Forum Thread:
How to Run and Install Kali Linux on a Chromebook
18
Replies
Forum Thread:
How to Run and Install Kali Linux on a Chromebook
18
Replies
5 mo ago -
 Forum Thread:
How to Find Admin Panel Page of a Website?
13
Replies
Forum Thread:
How to Find Admin Panel Page of a Website?
13
Replies
6 mo ago -
 Forum Thread:
can i run kali lenux in windows 10 without reboting my computer
4
Replies
Forum Thread:
can i run kali lenux in windows 10 without reboting my computer
4
Replies
6 mo ago -
 Forum Thread:
How to Hack School Website
11
Replies
Forum Thread:
How to Hack School Website
11
Replies
6 mo ago -
 Forum Thread:
Make a Phishing Page for Harvesting Credentials Yourself
8
Replies
Forum Thread:
Make a Phishing Page for Harvesting Credentials Yourself
8
Replies
6 mo ago
-
 How To:
Crack SSH Private Key Passwords with John the Ripper
How To:
Crack SSH Private Key Passwords with John the Ripper
-
 How To:
Exploit EternalBlue on Windows Server with Metasploit
How To:
Exploit EternalBlue on Windows Server with Metasploit
-
 How To:
Make Your Own Bad USB
How To:
Make Your Own Bad USB
-
 How To:
Scan Websites for Interesting Directories & Files with Gobuster
How To:
Scan Websites for Interesting Directories & Files with Gobuster
-
 How To:
Dox Anyone
How To:
Dox Anyone
-
 How To:
Create Custom Wordlists for Password Cracking Using the Mentalist
How To:
Create Custom Wordlists for Password Cracking Using the Mentalist
-
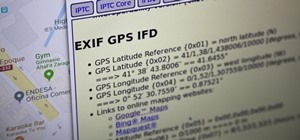
 How To:
Obtain Valuable Data from Images Using Exif Extractors
How To:
Obtain Valuable Data from Images Using Exif Extractors
-
 How To:
Create a Persistent Back Door in Android Using Kali Linux:
How To:
Create a Persistent Back Door in Android Using Kali Linux:
-
 How To:
Track a Target Using Canary Token Tracking Links
How To:
Track a Target Using Canary Token Tracking Links
-
 How To:
Scan for Vulnerabilities on Any Website Using Nikto
How To:
Scan for Vulnerabilities on Any Website Using Nikto
-
 How To:
Gain SSH Access to Servers by Brute-Forcing Credentials
How To:
Gain SSH Access to Servers by Brute-Forcing Credentials
-
 Hack Like a Pro:
How to Find Directories in Websites Using DirBuster
Hack Like a Pro:
How to Find Directories in Websites Using DirBuster
-
 How To:
Perform Advanced Man-in-the-Middle Attacks with Xerosploit
How To:
Perform Advanced Man-in-the-Middle Attacks with Xerosploit
-
 How To:
Use MDK3 for Advanced Wi-Fi Jamming
How To:
Use MDK3 for Advanced Wi-Fi Jamming
-
 How To:
Upgrade a Dumb Shell to a Fully Interactive Shell for More Flexibility
How To:
Upgrade a Dumb Shell to a Fully Interactive Shell for More Flexibility
-
 How To:
Find Exploits & Get Root with Linux Exploit Suggester
How To:
Find Exploits & Get Root with Linux Exploit Suggester
-
 Hack Like a Pro:
How to Use Driftnet to See What Kind of Images Your Neighbor Looks at Online
Hack Like a Pro:
How to Use Driftnet to See What Kind of Images Your Neighbor Looks at Online
-
 Hack Like a Pro:
Digital Forensics Using Kali, Part 2 (Acquiring a Hard Drive Image for Analysis)
Hack Like a Pro:
Digital Forensics Using Kali, Part 2 (Acquiring a Hard Drive Image for Analysis)
-
 How To:
Upload a Shell to a Web Server and Get Root (RFI): Part 2
How To:
Upload a Shell to a Web Server and Get Root (RFI): Part 2
-
 How To:
Create an Encryption Program with Python
How To:
Create an Encryption Program with Python















2 Responses
Well for your UAC problem I know 2 different exploits that could be used to bypass the uac. The first one respectfully called exploit/windows/local/bypassuac (in the Metasploit Console of course) can be used to bypass the UAC on both Windows 7 and 8. The second one is called exploit/windows/local/ask (also Metasploit) which brings up a menu for the victim to click OK on, but with this exploit the option that works best is the use TECHNIQUE PSH which is less likely to be caught by an antivirus. Bypassing UAC is also one of many known and unknown ways that will allow you to get system on Windows 7 and up.
Hope this helps
-TheVillain
A payload is a piece of code with the function of connecting you to a target ip (right?). Actually, OTW has a pretty neat tutorial explaining this and other concepts (here. So, a payload alone can't access anything (i think). As for bypassing uac, TheVillain explained it quite well i think!
Share Your Thoughts